This page brings together all of our articles on hosting, SaaS, cybersecurity, and related topics that affect how digital services work in real life. The focus is on practical understanding rather than technical detail: what things mean in everyday use, where common assumptions break down, and what tends to matter most over time.
The articles are written for founders, operators, and teams who want clarity without complexity. Topics range from infrastructure and pricing models to access control, data handling, and everyday security fundamentals.
-
 March 25, 2026
March 25, 2026Why your 8GB DIY VPS is Slower than a 2GB Managed Host: The Invisible Bottlenecks of CPU Steal and I/O Wait
You’ve likely seen the data: your site on a 4GB VPS is still lagging behind a competitor on a small managed plan. The reason isn’t -
 March 8, 2026
March 8, 2026Migrating From Shared Hosting To A VPS
Five Technical Issues That Commonly Break Sites Moving from shared hosting to a VPS is a natural step when a site becomes more important to -
 March 29, 2026
March 29, 2026Why “Unlimited Bandwidth” Is A Myth
Reading The Fine Print In SMB Hosting Terms Of Service Unlimited bandwidth is one of the most common hosting promises, and one of the most -
 March 25, 2026
March 25, 2026The True Cost Of DIY VPS
Calculating The Hourly Wage Of Your Own Server Maintenance A DIY VPS looks cheap on paper. You pay a small monthly fee, install what you -
 March 25, 2026
March 25, 2026Why Your VPS Load Average Is High Even When CPU Usage Is Low?
A Guide For SMB Owners If your VPS dashboard shows a high load average but CPU usage looks fine, it can feel like a false -
 March 29, 2026
March 29, 2026Is 2GB RAM Enough For A WooCommerce Site With 500+ Products?
For many WooCommerce stores, yes, 2GB can be enough. But it’s only enough if your traffic is moderate, your theme and plugins are not heavy, -
 March 7, 2026
March 7, 2026Why SSH Keys Are Safer Than Passwords For SMB Server Access
An ELI5 Guide For Business Owners If your team logs into servers using usernames and passwords, you’re relying on a security method designed decades ago. -
 March 7, 2026
March 7, 2026Why Your Home Router’s Built-In Firewall Isn’t Enough For A Permanent Remote Work Setup
Convenience Protection Isn’t Business-Grade Protection Most home routers advertise a built-in firewall. For everyday browsing and streaming, that’s usually fine. But when your home becomes -
 March 7, 2026
March 7, 2026How To Explain Least Privilege To A Non-Technical Marketing Team Without Slowing Them Down
Making Security Practical Instead Of Restrictive Least privilege sounds technical and restrictive. To non-technical teams, especially marketing, it can feel like a rule designed to -
 March 7, 2026
March 7, 2026The Export To CSV Trap
Why Manual Backups Aren’t A Real SaaS Exit Strategy Most SaaS products reassure customers with a simple promise: “You can always export your data.” On -
 March 7, 2026
March 7, 2026Why SaaS Vendors Gate API Access In Lower Tiers
And How It Quietly Limits SMB Automation If you’ve ever discovered that API access is only available on a higher SaaS plan, you’re not alone. -
 March 7, 2026
March 7, 2026The Hidden Cost Of Zombie SaaS
How To Identify Seats That Haven’t Logged In For 90 Days Before diving deeper, here’s what matters immediately. A zombie seat is a paid SaaS -
 March 7, 2026
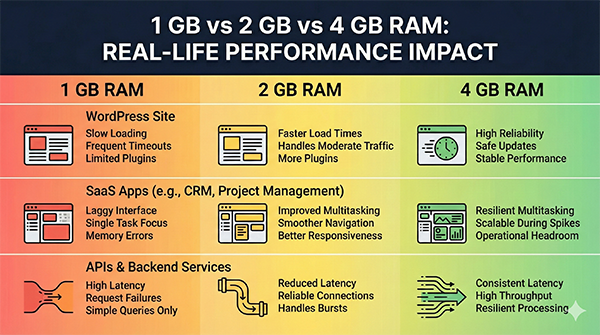
March 7, 20261 GB vs 2 GB vs 4 GB RAM: What Changes In Real Life
Why More RAM Doesn’t Always Mean Faster Beyond a certain point, additional RAM doesn’t directly improve performance unless the application can use it. The biggest -
 March 7, 2026
March 7, 2026What SaaS Outages Actually Look Like For Customers
Partial Failures, Slow Degradation, And Silent Data Issues When people imagine a SaaS outage, they picture a service that is completely down. In reality, most -
 March 7, 2026
March 7, 2026Password Managers Are More Important Than Firewalls: Why Identity Failures Cause Most Breaches
For decades, cybersecurity was visualized as a castle. You built high walls (firewalls) around your office to keep the bad guys out and the data -
 March 7, 2026
March 7, 2026What “Good Enough Security” Really Looks Like For B2B Teams
Clear Ownership, Boring Controls, Predictable Behavior Many B2B teams delay security because they picture it as expensive, complex, or disruptive. They assume real security requires -
 March 7, 2026
March 7, 2026The Myth of the Master Hacker: Why Most Breaches Begin with Neglect
When we imagine a cyber attack, we tend to picture a scene from a Hollywood movie: a hooded genius in a dark room, typing furiously -
 March 7, 2026
March 7, 2026Why Downgrading SaaS Is Often Harder Than Upgrading
What To Look For Before You Commit Before adopting a tool, ask what happens if you downgrade. Which features turn off, and how fast? What -
 March 7, 2026
March 7, 2026What Happens To Your Data When You Leave A SaaS
Assume that leaving a SaaS will be harder than joining it. Choose tools that make exits predictable, documented, and reasonably complete. A product that respects -
 January 27, 2026
January 27, 2026Choosing SaaS When You Don’t Want To Become A Power User
Tools For Teams That Just Want Things To Work Most SaaS products are designed to impress power users. They showcase endless configuration options, advanced workflows,